10 Tips for Remote Working for Software Development Teams (whether on a Daily Basis or in a State of Emergency)
As the COVID-19 or widely known as the Coronavirus is spreading around the world, more and more companies of any size and industry have no choice but to have their employees work remotely and preferably from home, sometimes even mandated by the governments themselves.
Compared to the state institutions or the manufacturing industry per se, the tech industry looks better equipped and more acquainted with remote working; but things are not as they seem. Especially in software development, the teamwork and collaboration are so crucial that many teams are specifically conceived for working together onsite.
Although the new generation of collaboration tools are working to alleviate the burden on physical presence, the core tools of software engineers have not yet caught up except a few innovative collaborative coding tools.
There are many technology start-ups as well as enterprises who successfully maintain a work from home culture with multi-location teams across geographies and even different time zones. Here are some tips as a guide to a successful telecommuting for software development teams, regardless of their technology stack.
1. Embrace the cultural shift
The current state of things regarding the virus outbreak is indeed unpleasant and the safety and the wellbeing of the employees overweighs any biases or concerns regarding remote working.
Even under normal circumstances, remote working has a positive impact on the wellbeing of the employees, which are usually overlooked.
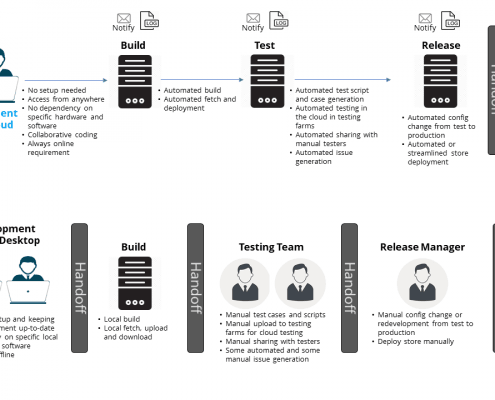
Of course, the shift does not happen just with the employees. The working environment is as crucial, so it also requires a shift in the technologies being used. In this sense, this is also an as an opportunity to realize the actual benefits of working in the cloud. Assess if and how you can shift the working environment to the cloud with the next generation solutions.
2. Overcome the negative bias about remote employees
There is a bias the employees will work less efficiently remotely. In certain industries such as manufacturing, that may be more applicable, but in the tech industry, the employees can be as productive as onsite with the right tools.
Remote presence tools such as chat and videoconferencing has been evolving for remote work from the cloud and now it is time for the core tools to follow.
Smartface Cloud IDE is one of the first of its kind to provide a full-featured Cloud IDE for mobile development and any other compatible technology stack such as JavaScript, TypeScript, Java, and .NET. It is not just a “browser-based editor”, but instead a cloud-powered development environment that employees can use remotely just as they would onsite.
3. Set up a platform-agnostic work environment
Due to the current circumstances, many enterprises are being obliged to take emergency actions to mandate working from home. However, the employees may be constrained with infrastructure limitations.
For instance, even if the employees are allowed to use their personal devices at home for work, their devices may be unsuitable due to the hardware or the software. (e.g. iOS development requires a Mac no matter what.)
The next generation cloud tools like the Smartface Platform aim to eliminate this dependency. Smartface Cloud IDE and Smartface Cloud CI/CD platform are fully independent from hardware and software. You can develop, build and deploy mobile apps anywhere and it works fine on low-end hardware as well.
Another benefit is the reduced battery consumption for the remote client. As the heavy lifting is offloaded to the cloud, the client consumes much less resources just to run the web browser instead of a heavy set of processes for an IDE.
Mobile development has one additional concern of running apps on mobile devices. When working onsite, the employees can utilize a common device pool, but working remotely requires an alternative solution to run mobile apps on multiple devices.
For this reason, we developed Smartface Preview on Device module. You can test your mobile apps just in your browser on multiple devices, no downloads or installation needed.
4. Utilize highly available and scalable solutions
Many enterprises provide ways of accessing the internal resources usually through the combination of VPN and remote desktop. However, both of these technologies have significant scaling challenges if the enterprises haven’t invested sufficiently on the infrastructure.
Remote desktop requires a steady and high bandwidth connection and even the slightest delay has a highly negative impact on the experience. When combined with VPN, the problem may be augmented, since a high-performance VPN requires a high capacity network infrastructure. In cases where all employees are working remotely just as we are facing now, the combination of VPN and remote desktop may not be up to the task.
Even if the VPN infrastructure is sufficient, there are challenges in configuration of the local clients and certain experience issues while taking over the full network traffic of the client.
Smartface Cloud IDE provides a much better experience than a remote desktop solution, with less dependency on the network stability and less bandwidth requirements. Moreover, the VPN can be handled on the server-side, putting less strain on the network.
Smartface Cloud IDE is a cloud-native solution and with its Kubernetes-based structure, it is highly scalable and available. All employees can work remotely with the same performance they can expect onsite.
5. Utilize collaborative solutions
Nowadays, most enterprises are using either Google Gsuite or Microsoft Office 365 for enterprise collaboration. For software development teams, tools like Atlassian JIRA and Slack are also following suit.
With remote working getting more prominent, these suites are getting more indispensable to remote access to resources as well as sharing and collaboration.
Smartface Cloud IDE enables enterprises to realize the benefits of the cloud collaboration for coding. Just like a Google Doc, developers can share their workspaces with others and work on the same project as if they are next to each other.
6. Implement strict guidelines and a structure
Another challenge of remote working is standardization. Especially, if the employees are using their own devices, it is highly problematic to manage a wide range of points from licenses to tooling standards.
Smartface Cloud IDE overcomes these issues with the pre-configured workspaces built for the enterprise specifications. The Cloud IDE can be used for many different technology stacks, including but not limited to JavaScript, Java and .NET.
The enterprise can prepare a specific workspace image and the all employees will have the exact same workspace when they load the Cloud IDE, regardless from where they access it.
7. Don’t let the tooling limit the flexibility
One thing that employees struggle when working from home is their personal setup if they are working on different devices. This may cause a loss in productivity from different aspects.
Smartface Cloud IDE provides the best of both worlds for this purpose. The developers can access the same environment just as they left it from any device. This minimizes the adaptation time and ensures that the developers are in their comfort zones where they are the most productive.
While Smartface Cloud IDE comes with pre-configured workspaces for the convenience of the enterprise, the IDE itself is fully customizable for the convenience of the developer. It is a full-featured IDE that matches desktop IDEs with features and experience.
8. Eliminate the pressure of demonstration of work
When working remotely, there is usually an untold pressure for the need to demonstrate that the employee is indeed working. Similarly, the supervisor is also concerned if the employee goes silent for a while.
Even the thought of this pressure distracts employees and reduces productivity. It is further intensified when the employees start focusing on “showing off work” instead of doing the actual work.
Smartface Cloud eliminates these concerns by providing various usage reports based on the Cloud IDE and CI/CD activities. The developers can focus on their work and the work shows itself with detailed reports.
9. Monitor, review and improve
Monitoring the productivity is not only crucial for the supervisors, but it is also important for establishing the remote work culture within the enterprise. The productivity numbers will help you see if there are any improvement areas to increase the productivity.
Smartface Cloud IDE reporting and auditing tools helps you make improvement decisions backed with numbers and if these decisions are related with technical improvements and changes, you can simply deploy a new IDE image and the updated IDE image will be available for everyone when they next launch their environment.
10. Realize the benefits and make the changes permanent
Whether through the circumstances or through a deliberate choice, you will have worked your way through the challenges of remote working with the help of best-in-class solutions like the Smartface Platform and you will be realizing the benefits.
- The boundaries are eliminated, the employees are still productive, and their work satisfaction increased.
- You can apply your learnings with employees to work with contractors or the third parties remotely as well.
- The supervisors still have the same level of visibility, if not more, with the help of detailed reports.
- Even if the nature of the business demands onsite work, you now have a backup option in case of emergencies.
The cloud-native architecture of the Smartface Platform for mobile development and CI/CD enables you to move your enterprise to the cloud with minimal dependency on onsite infrastructure for the shift to a remote working culture.
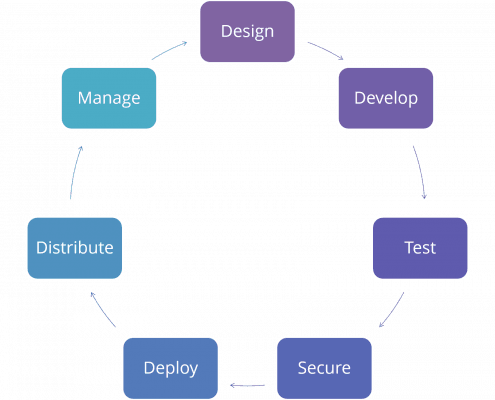
Smartface Cloud Platform is a fully cloud-based, cloud native, continuously integrated platform with multi-channel app development & lifecycle management and middleware & API management.
With Smartface, it is possible to develop native iOS/Android mobile and single-page web applications and mobile backends just with JavaScript/TypeScript knowledge and centrally manage all enterprise mobility and frontend management processes. The platform can run on compatible Kubernetes or OpenShift environments for the maximum flexibility.
You can get in touch with us for more information about the Smartface Platform.